Identity Server 2022.2 Release Notes
Former user (Deleted)
Former user (Deleted)
John Jellema
Release highlights
This release focuses on introduction of the following new features and improvements:
Directory User Mapped MFA for SAML and OpenID Connect methods
In this release we have extended the multi-factor authentication capabilities for SAML and OpenID Connect methods to include also OTP Printout, TOTP and OpenID Connect CIBA. This enables more MFA options for registered users in SSO that have enabled a Printout List, TOTP or CIBA to use OpenID Connect or SAML method as first factor - instead of the previous password method in SSO.
Administrators of SSO are able to set the configurations needed for their applications, for example - if they require to enter OTP code or if it optional for users that have set the method enabled for their account. For details please review the documentation here.
With the combination of previous Unregistered MFA SMS/SMTP and registered MFA SMS/SMTP/OTP List/TOTP/CIBA you can be sure that applications that require high assurance ask the user for an OTP code to access the service.
Logging
In this release we have fully replaced the logging solution used by SSO. This is part of the ongoing service maintenance of the Identity Platform and essential to ensure security and reliability while using Identity Server. We would encourage you to review the Logging - SSO page.
If you have not customised any logging features or implemented any tools for parsing the diagnostic logs, then the logging update provided will function similarly to prior releases with only simplifications in the location of the diagnostics logs for all applications installed on the same Tomcat server. Please ensure you review at least the Password reset and Password application sections as logging location and formatting has been updated.
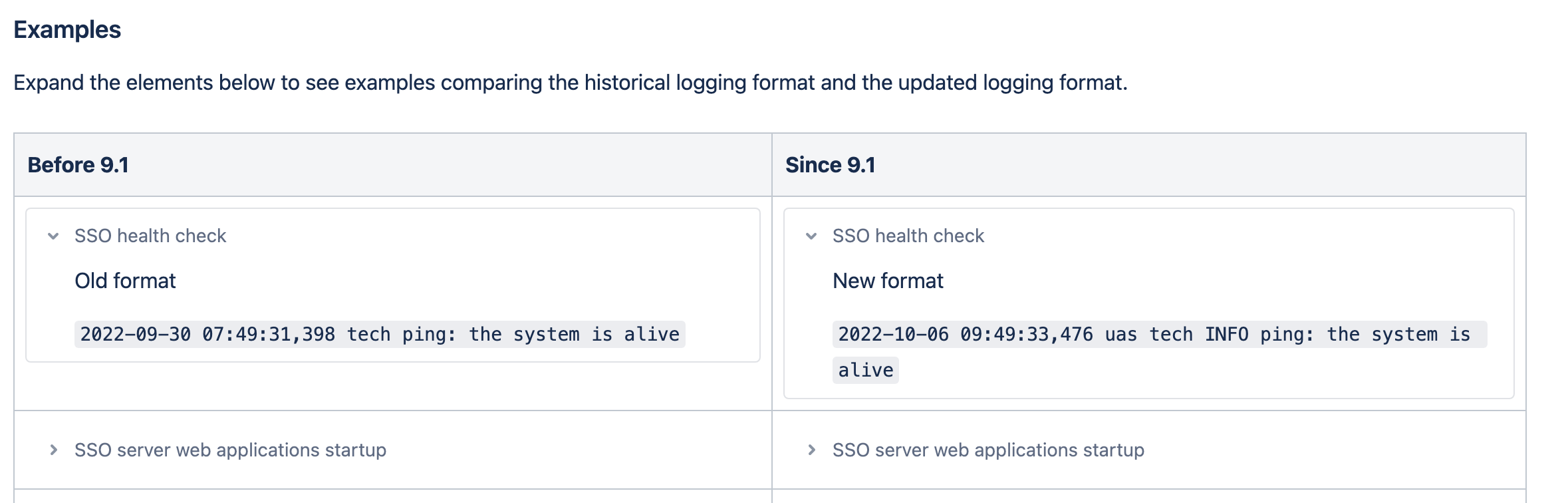
That said, there are differences in the location of the logs and formats of some log entries. We would strongly encourage you to review the comparisons table. The table shows examples for SSO versions up to 9.0.0 and with new logging used by SSO 9.1.0 and later. See the examples table - Logging migration guide - SSO.
Clicking the caret symbol next to each example will expose the details of each logging element.
Reform of personal identity code (SSN)
With the reform of Finnish personal identity codes that are coming into effect from 1st of January 2023 we have updated the CustomerID validation to make sure that both new and old SSN formats will be accepted.
More details about the reform can be found from the Digital and Population Data Service Agency.
Additionally, you will find a listing of known issues, with internal ticket references at the bottom of this page
Contents
Change log
SSO 9.1.0
New Features
- IDS-3494 - Logging for SSO webapps has been updated from Log4j to SLF4J and new logback.xml files are available for log configuration. All logs are now written to sso_diag.yyyy-MM-DD.log instead of catalina. Please ensure you review the Logging migration guide - SSO.
- IDS-3655 - SMS OTP, OTP Printout, TOTP and OpenID Connect CIBA can be used as multi-factor authentication for OpenID Connect and SAML methods when using Directory User Mapping. Configuration information can be found from Multi-factor Authentication with Directory User Mapping - SSO
- IDS-3817 - SMTP OTP (SPI SMTP) can be used as a multi-factor authentication for OpenID Connect and SAML mehtods when using Directory User Mapping. Configuration information can be found from Management UI authentication methods - SSO, SMTP authentication method - SSO and Unregistered Multi-factor Authentication - SSO
Improvements
- IDS-3694 - There is an update for the SAML SP for Java module (for Java 11) used to integrate web applications to SSO. Please review SAML SP activation - SSO.
- IDS-3578 - There is an improvement for TOTP logging level (to ALL). Please review TOTP API Configuration - SSO.
Corrections
- IDS-3745 - There was a known issue with id_token expiration times between application specific and server specific timeouts. If the application and server timeout is separate, the application specific expiration time will take the server timeout + application timeout as the id_token expiration time
- IDS-3767 - There was a known issue with Unregistered SMS or SMTP method used as second factor. If the method is not allowed for the intended group (not allowed for any group) or the configuration is left in a half configured state, then SSO shows ERROR 500 and a stack trace to the user
- IDS-3863 - There was a redirection vulnerability within the password-reset tool that permitted open domain, any URL, to be used as potential redirection. While there is no known instance of use of this deviation, we have resolved this by adding the ability to define allowed hostnames in returnurls.
- IDS-3871 - There was a redirection vulnerability within the password-reset tool that permitted cross site scripting to be post-pended to urls and used as potential redirection. While there is no known instance of use of this deviation, we have resolved this by adding the ability to define allowed hostnames in returnurls.
- IDS-1832 - There was a known issue where editing an existing authorisation policy (example case added an attribute) resulted in the alteration of ubiloginNameValue. This was corrected in other work found within SSO 8.6 and no longer impacts any supported version of SSO.
CustomerID 6.1.0
New Features
- None developed for this IDS 2022.2 release
Improvements
- IDS-3572 - SSN validation in CustomerID has been updated to also accept new formats of SSNs that are coming into effect in Finland from 1st of January 2023
- IDS-3872 - As part of ongoing maintenance, the PostgreSQL driver has been updated from 42.4.0 to 42.5.0
Corrections
- None required for this IDS 2022.2 release
Here you can find links to previous version's change logs for SSO and CustomerID
Known Issues
SSO
Ticket number | External description |
|---|---|
| IDS-561 | There is a known issue where SSO does not check the mappingURL value when creating or editing an inboundDirectoryMappings when using the SSO REST API. Directory Mappings are possible to be created, but then not opened or edited. |
| IDS-608 | There is a known UI/UX issue where a very large site list is displayed within the SSO management UI. This results in hard to use UI if large lists of sites are present in the SSO deployment. A possible workaround is to use an ldap editor to configure the authorization policies and groups. |
| IDS-941 | There is a known issue where unregistered SMTP OTP authentication will not permit TLS or any secure authentication. Documentation improvement will be made to ensure proper configuration is shown if unsecure SMTP servers are required. |
| IDS-1030 | There is a known issue where running the CertAP setup.cmd in a windows environment will post errors of missing linux tags. While these errors are unsightly, they can be safely ignored. This issue will be corrected in a future release. |
| IDS-1171 | There is a known issue when using OpenLDAP 2.4.44 when performing SSO session cleanup which will cause replication issues. |
| IDS-1499 | There is a known issue where SSO will return http 401, rather than http 400 when token introspection without an authentication header or when invalid credentials are present. |
| IDS-1525 | There is a known issue where SSO logs will contain a stopped search warning entry when tomcat is shutdown. This error can be safely ignored. |
| IDS-1526 | There is a known issue where SSO logs will contain a unstopped thread warning entry when tomcat is shutdown. This error can be safely ignored. |
| IDS-1629 | There is a known issue resulting in unclear error messages. When a user is configured without a phone number and SMS OTP method is added to their profile result in one of two error messages. If the SMS OTP is the only authentication method enabled, the message will be “The user account is disabled”. If there are other authentication methods enabled, the message will be “Access to the requested resource is denied”. |
| IDS-1635 | There is a known issue where the logout HTML of SSO contains two DOCTYPE entries. There is no known work around for this. |
| IDS-1648 | This is a known issue that only is only present with password2. User is presented with a popup "Update: Invalid account Status" if one of the previous three passwords are used when asked to update their password. There is no known work around. |
| IDS-1662 | The use of the following special characters when making any search will result in an internal sever error 500 and a stack trace. Symbols: + = # ; , < > Work around, administrators should not use the special symbols when naming users or searching for users. |
| IDS-1832 | There is a known issue where editing an existing authorisation policy (example case added an attribute) resulted in the alteration of ubiloginNameValue. This affects SSO 8.3.0 and later. There is no work around at this time. |
| IDS-1893 | There is a known issue if you use OpenID authentication, a user cannot access SAML or Ubilogin web applications. Work around use any other non-OpenID authentication method. If OpenID is required, then use OAuth 2.0 application. |
| IDS-1995 | When using BankID and Safari, during initial login Safari displays a 0kb file being downloaded when there is no downloaded file |
| IDS-2089 | There is a known issue where shutting down Ubisecure Accounting service on a windows server will show errors within the ids-accounting.log. |
| IDS-2090 | There is a known issue where the SSO management UI will not filter results correctly if the filter expression is short, contains incorrect filter expressions and there are Scandinavian characters included. |
| IDS-2092 | There is a known issue where the tomcat log will show a severe servlet warning for com.ubisecure.ss-ui. However, this warning is due to a user repeating the same action (double clicking an item or using the back button). This warning can be safely ignored and will be addressed in a future release. |
| IDS-2094 | There is a known issue where disabling the main account in the SSO login directory does not disable the User Driven Federation accounts. Users are still able to login to services with the Federated account even while the main account is disabled. Work around: Administrators who are disabling a main login directory account should ensure that they check and disable any associated UDF accounts at the same time. This issue will be addressed in a future release. |
| IDS-2095 | There is a known issue that the Acccounting service generates a temp folder under Ubisecure\ubilogin-sso\accounting\temp each time it is restarted. A workaround that system administrator can do is to create a cron job that removes these folders on a regular interval. |
| IDS-2096 | There is a known issue where attempting to use exceptionally long SAML Entity IDs will result in creation failure (larger than 64 characters) . There is no known work around and may not be possible to resolve due to LDAP field limitations. We will address this in a future release. |
| IDS-2120 | There is a known issue where dual node SSO will require jndi.properties to be manually configured on the second node during SSO upgrade. |
| IDS-2121 | There is a known issue where dual node SSO will require settings.sh to be manually configured on the second node during SSO upgrade. |
| IDS-2260 | There is a known installation issue when using SSO Password reset. Using the installation instructions for password reset tool requires an administrator to run tomcat update. This occasionally results in an empty context.xml file being created which causes SSO to fail when being restarted. Workaround, repeat the run tomcat update step which will create a correct .xml file and SSO will restart. |
| IDS-2261 | There are several known issues with javascript tools when using SSO Password reset. Similar javascript is used in UAS with no issue. If you are experiencing password reset javascript issue, please contact Ubisecure Support referencing this internal ticket for potential work arounds. |
| IDS-2314 | There is a known issue with passing a refresh token to token endpoint results in "invalid_grant" error, if the refresh token has been issued to an unregistered user from an authentication method having a connected Directory Service. |
| IDS-2315 | There is a known issue that SSO returns refresh token for un-registered users. This should not be done since there is no way of handling the lifecycle of the un-registered user's refresh token. |
| IDS-2332 | There is a known issue when using OpenLDAP in SSO where slapd runs out of connections to process incoming requests. |
| IDS-2478 | There is a known issue in SSO that it is not possible to have different localisations for access_denied returned by IdP and local access_denied, for example if directory user mapping fails after successful authentication |
| IDS-2663 | There is a known issue where creating a new site via a Safari browser where the site as an @ symbol in the email address will cause an error and no site will be created. This error is not experiences with current Chrome or Firefox browsers. As a work around please use one of these alternate browsers. |
| IDS-2790 | There is a known issue with sending in invalid formatted request to introspection endpoint returns stack trace including server version number. This can be mitigated by following our Security considerations for using reverse proxy and customising error pages with HAProxy Security considerations for production environments - SSO |
| IDS-2829 | There is a known issue that TOTP API is unable to generate secret for user if keysize has not been configured in the method. This is mitigated by ensuring that keysize is set when creating TOTP method. |
| IDS-2880 | There is a known issue when not including the scope of a sub claim in the authorisation policy for API protection. If this is not included during the API call, the response will not include any sub claims in the introspection response. A work around is to ensure your authorisation policy include the required claims. |
| IDS-2891 | There is a known issue if the Lockout Duration is set to 0, then no lockout time will be used ever. Work around is to set a very high number (in seconds) for accounts which should be locked out, but in a long duration. Remember to stop and start service for this configuration change to take place. |
| IDS-3092 | There is a known issue where Administrators are unable to alter password encoding through the SSO management UI. There is no known UI work around. |
| IDS-3113 | There is know issue after upgrading to SSO 8.8. If there were old Unregistered CIBA methods configured in the system, Administrators are unable to see the configuration information. To resolve this, Administrators are able to update the method Type from previous "Backchannel Authentication Adapter" to new "Unregistered OpenID Connect CIBA" type and restart SSO server. |
| IDS-3174 | There is a known issue within common-ubiutil that will return a an unescaped value where an escaped value is expected. This was identified during a misconfiguration, so is not expected to impact any operational environments. Work around is to ensure proper use of ldap names in configurations. |
| IDS-3186 | There is a known issue when changing password, if the current password is reused as the new password, an internal application error is shown. There is no known work around. Shown also as CustomerID known issue. |
| IDS-3625 | here is a known issue that an ERROR 500 message with stack-trace is shown in the browser if there is no valid encryption key available in SSO. Mitigation use reverse proxy to catch all 500 error with user friendly information Security considerations for production environments - SSO |
| IDS-3665 | There is a known issue where the authorisation endpoint may become corrupted if a URL contains "%20" in URL encoded format. |
| IDS-3730 | There is a known issue where using “Force Reauthentication” configuration for an application that uses refresh tokens, the refresh tokens are immediately invalidated. Workaround is to not use “Force Reauthentication”, set max age to 0 in auth request → Authentication is forced and refresh tokens are valid |
CustomerID
Ticket number | Description |
|---|---|
| IDS-693 | There is a known issue with user approvals from Users view. If there are required attributes for the approval step, these are not validated if approval is done through the Users view. |
| IDS-1332 | There is a known issue with CustomerID where it is not possible to use one email account for multiple UIDs created in CustomerID. Work around: It is possible for the system administrator to use custom attributes holding the same email address in the second or third CustomerID UID. |
| IDS-1358 | There is a known issue within CustomerID where an administrator applying permissions across a whole organization will result in a failure of CustomerID to initialise. Work around: Admins should ensure that they do not apply permissions to an entire organisation, but apply the permission to a specific organisation class. All classes within an organisation may have the permission added, but not to the whole organisation at the same time, during the same commit. |
| IDS-1365 | There is a known UI improvement for lists of Users and Roles for CustomerID administrators. Currently the lists are not ajax based, which means that cannot be called via popup, unlike other lists seen in CustomerID Admin UI. While this does not cause an error, it is not ideal from a usage point of view. |
| IDS-1373 | There is a known issue in CustomerID when a new user is created in a non-virtual organisation, the invitation can contain a role when no role has been approved for that user. |
| IDS-1380 | There is a known issue with CustomerID organisational attributes where the UI validation (validation.json) is not utilised. This impacts MOD001, POST100, PUT101 and MOD003. Using the API calls will result in good responses, but no organisational attribute change will be made. |
| IDS-1382 | There is a known issue within CustomerID mandates where no email is sent to the user or organisation when the configuration is set to false ( mandate.receiver.approval = false), even though the administrator requests a mail to be sent. No error or warning screen is displayed. |
| IDS-1389 | There is a known usage limit in CustomerID Mandates. When viewing a mandate, currently only the role is shown. It would be more user friendly to show both the role and its organisation within the mandate view. There is no workaround. |
| IDS-1411 | There is a known issue within the CustomerID XML schema ID, if an administrator makes an error and reuses and existing variable ID, this second use of the variable ID will not be assigned but the organisation will still be created. No error is reported. This can cause troubleshooting and usage errors. Workaround: Administrators should ensure that variable IDs are unique prior to creating new variable IDs within the system installation. |
| IDS-1413 | There is a known error in CustomerID mandates if the mandate name is longer than 61 characters. If longer than 61 characters, creating the mandate will fail. Workaround: Do not create mandate names longer than 61 characters. |
| IDS-1418 | There is a known issue with CustomerID REST API MOD008. If an administrator removes a single mandate role from a user with multiple mandate role, the original (removed) mandate template still exists within the LDAP database. This can result in troubleshooting errors and database checking errors (backup, etc). |
| IDS-1419 | There is a known issue with CustomerID REST API MOD021 when creating a new user. Even when the API call appears to work, the user is not added to the organisation. Workaround: Do not use REST MOD021 (modification) during the creation of a new account. Please ensure you use create APIs when making new users. |
| IDS-1446 | There is a known issue when using CustomerID REST API MOD009 to create a new user. The API will return 200 OK even when the new user password is not set; this results in a failed account creation. Workaround: Do not use REST API MOD009 (modification) to create a new user account. Please ensure you use create APIs when making new users. |
| IDS-1463 | There is a known issue when using the CustomerID lost password recovery wizard where the wildfly server will log an exception in the error log. The password reset works correctly for the end user, but the resulting log file is cumbersome for large deployments where end users often reset their passwords. The error exceptions can be safely ignored, these will be corrected in a future release. |
| IDS-1468 | There is a known issue caused by an Administrator altering the name of an Organisation when a new user has registered but not yet been approved. An application error occurs and is logged. Workaround: To avoid this only change an organization name when the pending user view is empty. |
| IDS-1474 | There is a known issue that results in unsaved organisational custom attributes occurring when approval is set to false; attributes are saved when they should not be. |
| IDS-1476 | There is a known issue within User DrivenFederation (UDF) of a social login during registration. If a user attempts to register more than one social login (UDF) against an external account a warning error message is presents. Resolution will be to provide the user a message explaining that they have already UDF'd a social account to this internal account and it is not possible to register a second social account. |
| IDS-1478 | There is a known issue that results in a null pointer exception with stack trace if a user attempts Self Service User Driven Registration (UDF) of a social login account when UDF is not enabled within the CustomerID service. |
| IDS-1494 | There is a known issue that causes occasional error pages to be displayed when a user logs out of their federated (User Driven Federation, UDF) social login account. |
| IDS-1504 | This known issue is a regression. When a user is invited to multiple roles, only one role appears in the invitation screen. This impacts both CustomerID Admin UI and user Self-Service. |
| IDS-1509 | There is a known issue where a new user being invited to a virtual organisation the CustomerID administrator cannot approve the user; an internal server error occurs. |
| IDS-1555 | There is a known issue where the mandate tab cannot be accessed on the CustomerID UI if the localisation information is incomplete. Workaround is to ensure that all localisation fields are completed. |
| IDS-1681 | There is a known issue where the cursor focus remains in the mobile text field after a user has selected the email confirmation, when both email and mobile confirmations are required. |
| IDS-1706 | There is a known issue with null values (DbAssignable.set and DbAssignable.isNull) which may result in NullPointer exceptions when using REST calls. This impacts Roles, Mandates and Invitations. |
| IDS-2033 | Search response when using the CustomerID authoriser rule will return duplicate entries if capitalisation is present in the searched term or in the database field. In the future, no duplicates will be returned even if capitals are used or present in the naming field. Example: friendlyName and friendlyname. |
| IDS-2091 | There is a known issue that the "New Organization" field in the "Open user applications" approval tab sometimes shows incorrect status |
| IDS-2093 | There is a known issue that listing of users doesn't take into considerations users that are in locked status |
| IDS-2162 | There is a known issue in CustomerID within Mandates, where no renotify email is sent to the administrator when an existing user requests a mandate for an existing additional organisation. No email is sent to Administrators for approval and no errors are logged. There is no workaround for this issue. |
| IDS-2201 | There is a known issue in CustomerID where an email to a user with a single expiring or expired role will have all open roll invitations listed in the email, not just the expiring or expired role invitation. |
| IDS-2205 | There is a know issue in user registration where the "Mobile input field was not confirmed" error message is left in the UI even after the user has verified their mobile number if they have other invalid fields to correct |
| IDS-2207 | There is a known issue in CustomerID where interrupting the creation of a pending user will reset localisation of the browser session. |
| IDS-2231 | There is a known issue when Administrator denies a role request for a user, that user gets two emails sent to them. One stating "Role invitation denied" and a second one stating "Role denied". |
| IDS-2233 | There is a known issue in CustomerID API 1.2 REST call MOD025 "Create Role Invitation" related to email notification. If this REST call is used, the inviter mail address configured does not get a notification when the end-user approves the received role. The notification still works if role invitations are done through the GUI. |
| IDS-2290 | There is an issue opening approval tab under main organization branch if there are around 10 000 sub-organizations. As a workaround, you can choose not to use recursive selection by adding "admin.approvals.recursive.selection.default = false" to you eidm2.properties file. See also: IDS-2310 below. |
| IDS-2310 | There is an issue searching roles under main organization branch if there are around 10 000 sub-organizations. As a workaround, you can choose not to use recursive roles by adding "ui.organization.roles.recursive = false" to you eidm2.properties file. See also: IDS-2290 above. |
| IDS-2311 | There is a known issue in approval view where changing main organization for a pending user in a sub-organization fails to create the new sub-organization in LDAP. This will need to manually be resolved by removing the invalid sub-organization in SQL |
| IDS-2312 | There is a known issue in approval view where changing technical name of an organization to include Scandinavian letters doesn't work. |
| IDS-2420 | There is a known issue in registration when pressing Enter without filling in all required fields causes registration to get cancelled instead of highlighting the required fields needed to complete the registration. Identified in CID 5.3.5 |
| IDS-2683 | There is a known issue where CID REST API's 2.0 and 2.1 do not locate organisations with URL encoded characters in their names. Work around, if possible, ensure there are no URL encoded characters within organisation names. (example Ä Ö Å). |
| IDS-2703 | There is a known issue where a role name with different case can be created which results in one LDAP entry and two SQL entries. |
| IDS-2712 | There is a known issue where an internal error is shown and stack trace is logged when a user registers with the same organisation name as an existing organisation but in a different case. Example. "UBISECURE" when "Ubisecure" already exists. |
| IDS-2713 | There is a known issue impacting Windows server installations, where the import and export tools fail to move users between CustomerID 5.3.x and later versions. |
| IDS-2814 | There is a known issue where Self Service will not open a user control window if the UDF (user driven federation) link refers to an obsolete authentication method. For example if the external identity has switched from SAML to OIDC. An exception is presented. There is no work around at this time. |
| IDS-2816 | There is a known issue which will create an unhandeled exception if the users SMTP server cannot be resolved. This issue will cause a database collision issue which may prevent the same email address from being used, as it already exists within the database but not in a fully created form. |
| IDS-2876 | There is a known issue if user is rejected from UI error is logged "Error when trying to get approval request with ID: null". A stack trace is logged. This stack trace can be safely ignored. |
| IDS-2891 | There is a known issue if the Lockout Duration is set to 0, then no lockout time will be used ever. Work around is to set a very high number (in seconds) for accounts which should be locked out, but in a long duration. Remember to stop and start service for this configuration change to take place. |
| IDS-2930 | There is a known issue that CustomerID REST API returns invalid response code for internal server errors. If there is an internal server error, CustomerID REST API now returns 404 Not Found instead of 500 Internal Server Error. |
| IDS-2934 | There is a known issue in CustomerID within Mandates, where no renotify email is sent to new user to register using mandate invitation. Admin user sends mandate from Admin UI to new user that is not registered to the system. Email is sent correctly, but no renotify is sent to register to the system.Mandate expires correctly also and email is sent that mandate was expired. |
| IDS-2936 | There is a known issue with data.attribute.mapping.surname = sn when using OpenLDAP. The attribute mapping will not occur. |
| IDS-2941 | There is a known issue where a NPE will occur if an administrator is viewing an ORG2PER mandate from the CustomerID management UI. |
| IDS-3058 | There is a known issue where in change password application of CustomerID where the return URL is missing a forward slash (returns "https:/" not "https://") resulting in failed redirect if the cancel button would be enabled. |
| IDS-3186 | There is a known issue when changing password, if the current password is reused as the new password, an internal application error is shown. There is no known work around. Shown also as SSO known issue |
| IDS-3206 | There is a known issue where a user is completed registration and is waiting for approval of registration. No email is sent to any administrator that there is registration that needs to be approved. |
| IDS-3339 | There is a known issue where it is not possible to create person to person (PERTOPER) or person to organisation (PERTOORG) mandates from the CustomerID UI. Work around this limitation by using REST API's which do permit these mandates. |
| IDS-3392 | There is know issue when Administrator moves user is used moved to another organisation then error is logged. The user is moved correctly, but unnecessarily logging occurs. The log entries can be safely ignored. |
| IDS-3483 | There is a known issue with GET113 List Organization's Users API call. When adding parameter ?status=Enabled the call returns Internal error |
| IDS-3698 | There is a known issue with rejecting a user registration that doesn’t remove the approval request from the CustomerID database. A workaround for this is to remove the pending approval request from the database |
| DS-3727 | There is a known issue with email validator in regards to case-sensitive emails. For example user@email.com and User@email.com are treated as different emails. To fix this;
|
| IDS-3765 | There is an issue with JDK 11.0.15 that prevents Wildfly from working |
Considerations and limitations
SameSite cookie changes in Google Chrome
In Google Chrome version 80 and above, the default behaviour of cookies that are used in cross-domain use cases have changed. If your applications or services are communicating between different top-level domains you need to take the following actions as described in our SameSite cookies changes technical announcement to ensure that they continue to operate as before.
Long Certificates Require Manual Installation in Linux Version
When a certificate is set in suffix.pfx, whose base64 encoded string is longer than about 4000 characters, the installation of SSO ends in a failure. This is due to an issue with an OpenLDAP tool ldapmodify, which is unable to read lines longer than 4096 characters long and the installation script writes the base64 encoded certificate in one line in secrets.ldif. To address this issue, a tool ldiffold.sh was included with SSO 7.1.0 linux version, which wraps given ldif file so that it no longer contains lines that are too long. It can be run as follows:
cd /usr/local/ubisecure/ubilogin-sso/ubilogin/ldap ../../tools/misc/ldiffold.sh < secrets.ldif > secrets.ldif.tmp mv -f secrets.ldif.tmp secrets.ldif
Ubilogin Ticket Protocol Attribute Size Limits
The Ubilogin Ticket Protocol uses the HTTP GET method to send authentication and authorization information from UAS to Web Agents. The HTTP GET method has a size limit. The size limit affects the amount of information it is possible to successfully send from UAS to Web Agents. The SAML 2.0 protocol resolves this size limit by using the HTTP POST method to send information from UAS to Web Agents.
Ubilogin SAML Service Providers use SAML 2.0 protocol.
Ubisecure SSO, SAML 2.0 and High Availability
When installing Ubisecure SSO in High Availability mode, there are some restrictions due to some protocol requirements when using SAML 2.0. Please refer to the Ubisecure Clustering document for more information.
Backwards compatibility issues
Swedish BankID Authentication Adapter
For installations of SSO 8.4.1 through 8.7.0, the Swedish BankID Mobile authentication adapter has to be configured using the JWKS key id (kid) exposed in the SSO JWKS metadata. See Installing and configuring Swedish BankID - SSO for more details. It should be noted that Swedish BankID have altered several details of their authenticator, as we strongly recommend using their latest application.
To use all current Swedish BankID features and functions, you are required to use SSO 9.0.0 with CIBA authenticator 2.0.0.
SQL directory and OTP printout or TOTP
With SSO 8.8.0, if you have users coming from SQL directory and you are using OTP printout or TOTP, you need to add LegacyUserCredentialsTable compatibility flag to the method and restart SSO server to make sure it takes affect.