Management UI authentication methods - SSO
Contents
Methods (Server) (Home → Global Method Settings) represent the authentication methods of Ubisecure SSO. This view differs from the methods views in sites and is only available for the System Administrator. Site Managers have no access to this Global Method settings configuration view.
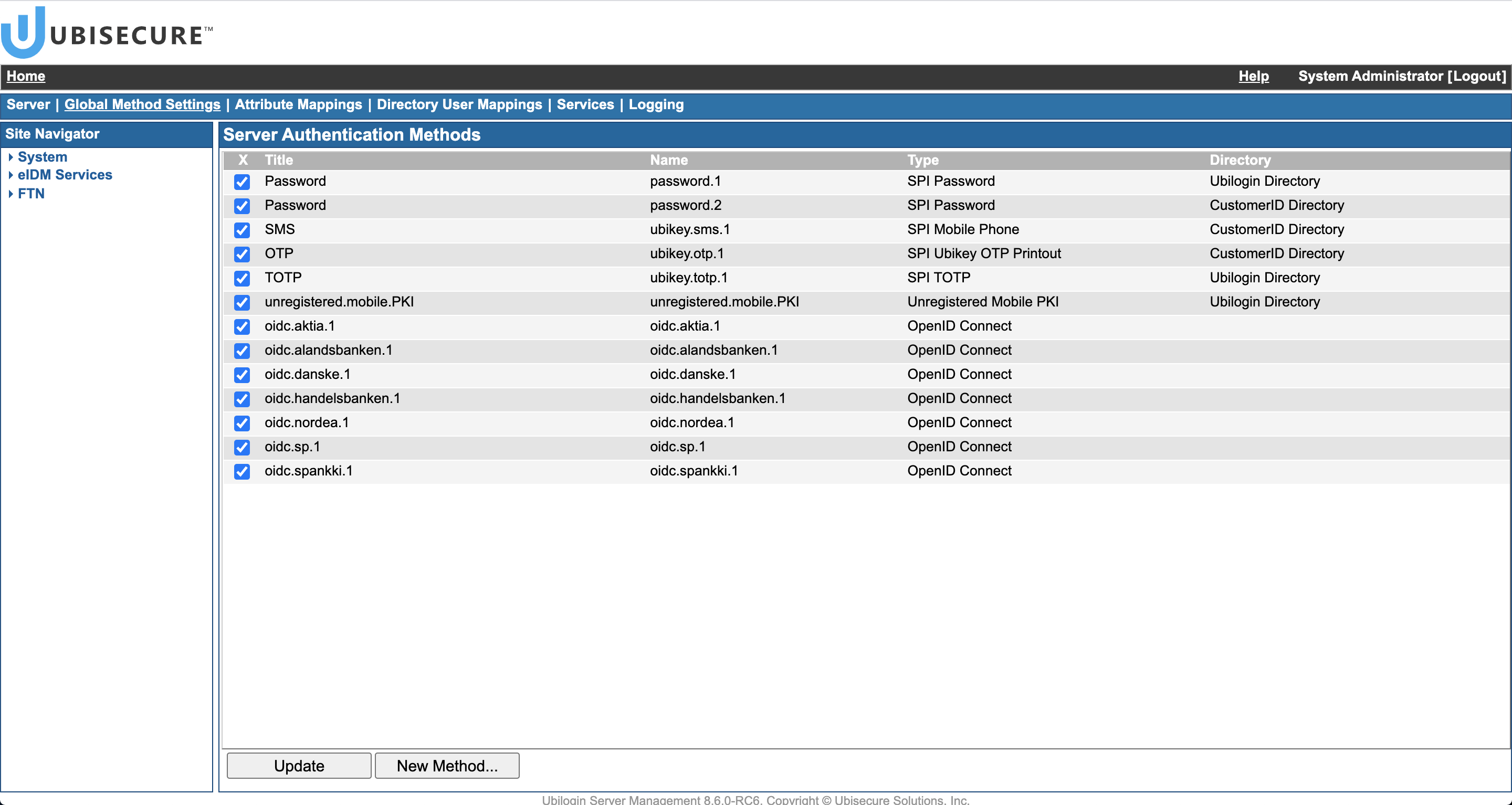
The global method settings view (Figure 1) lists all of the Ubisecure SSO authentication methods that are currently installed in Ubisecure SSO.
| Figure 1: The Ubisecure SSO authentication methods view |
- Update
By selecting the authentication method check box and clicking Update System Administrator can enable or disable the selected methods in Ubisecure SSO. - New Method…
By clicking the New Method… button System Administrator can add new authentication methods to the system. - Authentication Method
By clicking each type of authentication method the System Administrator can configure the selected authentication method. The configuration view consists of the following sub menus: Main, [authentication method type], Mappings, Sites, Applications, Groups
There are different types of authentication methods that Ubisecure SSO supports out-of-the-box:
- SPI Password
- SPI Mobile Phone (SMS)
- SPI TOTP
- SPI OTP Printout
- SPI Mobile PKI ("Mobiilivarmenne" in Finland with using pre-registered account information)
- SPI OpenID Connect CIBA
- Unregistered Mobile Phone (SMS, without password)
- Unregistered SMTP (email, without password)
- Unregistered MPKI
- TUPAS 2 (Finland)
- SAML Authentication Provider
- Authentication Provider (Ubiticket Protocol)
- OpenID
- OAuth 2.0
- OpenID Connect
- OpenID Connect CIBA
Additional methods are used to configure discovery service settings:
- Third-party SAML Discovery Service
- Common Domain Cookie Discovery
Please refer to additional method installation guides for specific configuration instructions.
Main view
| Figure 2: Configuring password authentication method |
- Title
The title of the authentication method is visible for end-users in the login pages and for administrators in the Ubisecure SSO Management application. - Name
The name of the authentication method is provided by the Web Application to the web servers and web applications. - Type
This contains the technical type of the authentication method. This value will change depending on the integration technique used. Read-only value. - Class
This contains the java class of the authentication method. This value will change depending on the integration technique used. Read-only value. Used particularly for identifying custom authentication methods. - Directory
The directory that the authentication method uses. Directory can be set and changed only through the directory configuration, see Selecting directory for an authentication method.
- SAML 2 Declaration Reference
The qualified name for the authentication method that is used in SAML protocol messages to refer specifically to this method. This mandatory value is automatically generated and cannot be modified. This value is unique to each authentication method.This value is used in response messages to set the AuthnContextDeclRef value of the AuthnContext element of the AuthStatement.This value is used to determine which method satisfies a requested authentication context declaration reference (RequestedAuthnContext) in an incoming AuthnRequest.
- SAML 2 Class Reference
Defines the URI of the authentication method class.
This field is optional. Some federation networks or third-party products may require a value. It is used in the SAML protocol messages to refer a group of authentication methods that share similar properties. This value is not unique to each authentication method – the same value may be assigned to many similar methods.This value is used in response messages to set the AuthnContextClassRef value of the AuthnContext element of the AuthStatement. Authentication Context Classes are defined in Section 4.3 of the Authentication Context for the OASIS Security Assertion Markup Language (SAML) V2.0 http://docs.oasis-open.org/security/saml/v2.0/saml-authn-context-2.0-os.pdf
This value is also used to determine which methods satisfy a requested authentication context class (RequestedAuthnContext) in an incoming AuthnRequest. This is used to determine which method or methods will be available to the user for login.
Typical class references used includeurn:oasis:names:tc:SAML:2.0:ac:classes:MobileTwoFactorUnregistered urn:oasis:names:tc:SAML:2.0:ac:classes:MobileTwoFactorContract urn:oasis:names:tc:SAML:2.0:ac:classes:PasswordProtectedTransport urn:oasis:names:tc:SAML:2.0:ac:classes:X509 urn:oasis:names:tc:SAML:2.0:ac:classes:Smartcard urn:oasis:names:tc:SAML:2.0:ac:classes:SmartcardPKI urn:oasis:names:tc:SAML:2.0:ac:classes:SoftwarePKI urn:oasis:names:tc:SAML:2.0:ac:classes:unspecified
Selection of the appropriate class reference depends on many configuration factors and deployment profile guidelines.
- By default, if no value is set, the AuthnContext element of the AuthStatement will not contain AuthnContextClassRef value.
- OpenID Connect Authentication Context Class Reference
Defines the value of the OpenID Connect The Authentication Context Class. This field is optional. It is used in the OpenID Connect protocol messages to refer a group of authentication methods that share similar properties. This value is not unique to each authentication method and the same value may be assigned to many similar methods.This value is used in userinfo response message and idtoken to set the value of acr claim.
This value is also used to determine which methods satisfy a requestedacr_valuesin an incoming authorization request. This is used to determine which method or methods will be available to the user for login.
- Format
This setting is used for claims transformation and validation. Generally these are not required and may be left blank. It can be used for interoperability with connected applications that expect NameID format value to be in a certain format and to enforce compliance with federation profiles.
Technically this sets or confirms the value of the attribute Format in SAML message NameID element.- set value → Overwrites the Format value received from an authentication to Format specified. For example, if the assertion received from a third-party authenticator contains a NameID Format value Transient, it can be changed to unspecified.
- Note, NameID Format value can also be overwritten at the application level by using an Authorization Policy containing expression language statement:
${nameID.value( user.cn ).format(‘x509subjectname’)}
- Note, NameID Format value can also be overwritten at the application level by using an Authorization Policy containing expression language statement:
- assert value → Verify that the value of the attribute Format is equal to the specified value. If the value is something else, the authentication is denied and the user is shown an error message.
- Example: If the connected application requires that the NameID format to be email address format, and will fail if not, set "assert emailAddress" to check the value and fail if not does not match "emailAddress".
- any → For built-in authentication methods, use the default value for the attribute Format. For external/proxy methods, use the Format value in the received NameID/username. (This is the default behaviour when Format field is empty)
- unspecified - The interpretation of the content of the element is left to individual implementations.
- transient - Indicates that the content of the element is an identifier with transient semantics and SHOULD be treated as an opaque and temporary value by the relying party.
- persistent - Indicates that the content of the element is a persistent opaque identifier for a principal that is specific to an identity provider and a service provider or affiliation of service providers.
- emailAddress - Indicates that the content of the element is in the form of an email address, specifically "addr-spec" as defined in IETF RFC 2822 Section 3.4.1. An addr-spec has the form local-part@domain. Note that an addr-spec has no phrase (such as a common name) before it, has no comment (text surrounded in parentheses) after it, and is not surrounded by "<" and ">".
- X509SubjectName - Indicates that the content of the element is in the form specified for the contents of the <ds:X509SubjectName> element in the XML Signature Recommendation. Implementors should note that the XML Signature specification specifies encoding rules for X.509 subject names that differ from the rules given in IETF RFC 2253.
- WindowsDomainQualifiedName - Indicates that the content of the element is a Windows domain qualified name. A Windows domain qualified user name is a string of the form "DomainName\UserName". The domain name and "\" separator MAY be omitted.
- encrypted - The special Format value urn:oasis:names:tc:SAML:2.0:nameid-format:encrypted indicates that the resulting assertion(s) MUST contain elements instead of plaintext. The underlying name identifier's unencrypted form can be of any type supported by the identity provider for the requested subject. See SAML Core 3.4.1.1.
- kerberos - Indicates that the content of the element is in the form of a Kerberos principal name using the format name[/instance]@REALM. The syntax, format and characters allowed for the name, instance, and realm are described in IETF RFC 1510.
- entity - Indicates that the content of the element is the identifier of an entity that provides SAML-based services (such as a SAML authority, requester, or responder) or is a participant in SAML profiles (such as a service provider supporting the browser SSO profile).
Note that using this feature to set the Format attribute of the NameID does not validate that NameID conforms the specifications explained above. For example, the format of a NameID containing an email address as its content can be set to X509SubjectName here, even though it does not conform the specification of X509SubjectName. - set value → Overwrites the Format value received from an authentication to Format specified. For example, if the assertion received from a third-party authenticator contains a NameID Format value Transient, it can be changed to unspecified.
- NameQualifier
Set or assert the value of the NameQualifier attribute in SAML message NameID elements.
- SPNameQualifier
Set or assert the value of the SPNameQualifier attribute in SAML message NameID elements.
- Enabled
Enable or disable the authentication method in Ubisecure SSO. - Hidden
Hide this authentication method. The authentication method is never visible in the authentication method selection menu. The method can only be selected when requested by a Web Application. Limit Method Visibility
Set the visibility for this authentication method by a list of network addresses separated by a space character ' '. The method is visible in the menu only if the client's network address is within any of the defined networks. If this field is empty, the method is visible to users from all network addresses. Example:192.168.1.0/255.255.255.0 10.1.1.0/255.255.255.0
→ The method is visible only if the client's network address is in either of the two private networks
Some authentication method types such as Password, OTP Printout and Mobile Phone have also the following configuration fields for Account Lockout Policy.
- Lockout Threshold (attempts)
Specify the number of tries that a user gets to enter in an incorrect password before the account becomes locked out for the time specified below. The default value is five attempts, if the field is left empty. (default value 5) - Lockout Duration (minutes)
Specify the number of minutes a locked out account remains locked out before automatically becoming unlocked. You can specify that the account will be locked out until a System Administrator or a Site Manager explicitly unlocks it by setting the value to 0. (default value 20min) - Configuration String
Name-value properties that can be used to configure method settings that do not have a user interface yet.
Mappings View
The names of the method attribute mapping and directory user mapping tables assigned to the method are shown in the Mappings context window. Refer to the chapters below for more information about assigning and unassigning the mapping tables to the methods.
- Method Attribute Mapping Table
Name of a method attribute mapping table assigned to the method. Attribute mapping table may be accessed by clicking the name. If an attribute mapping table is assigned to the method, only the mapped attributes are available for authorization policies and web applications. If no attribute mapping table is assigned, all method attributes are available. - Directory User Mapping Table
Name of a directory user mapping table assigned to the method. Directory user mapping table may be accessed by clicking the name. - SOSO Configuration
Name of a SOSO configuration assigned to the method. SOSO configuration may be accessed by clicking the name.
Sites View
| Figure 3: Sites view in Ubisecure methods configuration |
The Sites view gives you the list of the Ubisecure sites where the selected authentication method is visible and available.
- Remove
Select the Sites' check box and click Remove to remove this authentication from the selected Ubisecure Sites
Applications View
| Figure 4: Applications view in Ubisecure SSO methods configuration |
The Applications view gives you a list of the Ubisecure Applications where the selected authentication method is in use.
- Remove
Select the Applications' check box and click Remove to remove this authentication from the selected Ubisecure Applications
Groups View
| Figure 5: Groups view in Ubisecure SSO methods configuration |
The Groups view gives you the list of the Ubisecure Groups which members are all of the unregistered users that are authenticated with the selected authentication method. In the example above, users authenticating with the method tupas.nordea.1 will be assigned membership to the group TUPAS users. Adding a group to this list is done from the method tab of the Group view.
Unregistered users are users that are not in the Ubisecure Directory or in an external directory but are authenticated using an external authentication service.
- Remove
Select the Groups' check box and click Remove to remove this authentication from the selected Ubisecure Groups
Authentication Method Types
The next chapters present the specific configurations for each authentication method type.
SPI Password
The Password authentication method validates users against the current system's Ubisecure Directory . Ubisecure SSO maintains the password expiry and lockout policy based on the Lockout Threshold and Lockout Duration settings in the Main tab.
| Figure 6: Configuring SPI Password authentication method |
- Password encoding
Define the name of the one-way hashing algorithm that is used to store passwords in the Directory Service used by the password Authentication Method.- Supported values: {BCRYPT}, {SSHA512}, {SHA512}, {SSHA384}, {SHA384}, {SSHA256}, {SHA256}, {SSHA}, {SHA}, {PKCS5S2}, {PBKDF2-SHA256}, {PBKDF2}, {MD4}, {PLAIN}
- An empty value means that the default password encoding of the Directory Service is used. For example, for SQL it is {SSHA} and for Ubisecure Directory it is {SSHA}. Please consult the specific Directory Integration guide for the default password encoding.
- For Active Directory integrations, the encryption configuration of the Active Directory instance is used explicitly and the value set here is not used.
Password Policy Enhancements
It is possible to tighten password policy further by using any of following settings in the Configuration String section:
- policy.password.min-age
Minimum age of password in minutes before password can be changed again.
- policy.password.max-age
Maximum age of password in minutes, when exceeded user is forced to change it.
- policy.password.history
Number of password history entries to keep.
- policy.password.charset
Allowed character set of password. Generally recommended values are either ASCII or UTF-8.
- policy.password.length
Minimum required amount of characters in password during password change or reset operation.
- policy.password.complexity
If true, then user must enter 3 out of 4 types of characters: 1) numbers, 2) special characters 3) upper case letters 4) lower case letters.
- policy.password.expiring
Time in minutes before password starts to expire. When this threshold is exceeded, the user will be notified of impending password expiration and password change is offeredTime in minutes before password max-age is reached. When this threshold is exceeded, the user will be notified of impending password expiration.
External Password
External Password authentication method has been deprecated and replaced by the SPI Password method. Use directory.account.login property to configure the attribute by which users are identified in the external directory. Link the SPI Password method to some directory service that configures a connection to an external directory.
External Password methods are described in more depth in the guide External directory integration - SSO. Please refer also to the following individual guides:
Authentication Provider
The Authentication Provider authentication method type is used for configuring the Windows Single Sign-On authentication method, which uses Windows Authentication Provider software component.
The configuration window for Authentication Provider type authentication method is presented in Figure 7.
| Figure 7: Configuring Authentication Provider type of authentication method |
Please refer to page Windows Authentication Provider - SSO for more details on installing and configuring the Windows authentication method.
SPI Mobile Phone
The configuration window for Mobile phone type of authentication method is presented below.
| Figure 8: Configuring SPI Mobile Phone authentication method |
Please refer to SSO Installation Appendix - SMS for installing and configuring the Mobile Phone authentication method. If Mobile Phone method is used in conjunction with an external directory, please refer to one of the following guides:
- External directory integration - SSO
- Active Directory integration - SSO
- Basic LDAP integration - SSO
- Schema enhanced LDAP integration - SSO
- SQL integration - SSO
Unregistered Mobile Phone
The configuration window for Unregistered Mobile Phone type of authentication method is presented below. Configuration parameters in the bottom of the page.
| Figure 9: Configuring Unregistered Mobile Phone authentication method |
Please refer to SSO Installation Appendix - SMS for installing and configuring the Unregistered Mobile Phone authentication method.
Unregistered SMTP
The configuration window for Unregistered SMTP type of authentication method is presented below. Configuration parameters in the bottom of the page.
| Figure 10: Configuring Unregistered SMTP authentication method |
Please refer to Appendix - Unregistered SMTP Authentication Method for installing and configuring the Unregistered SMTP authentication method.
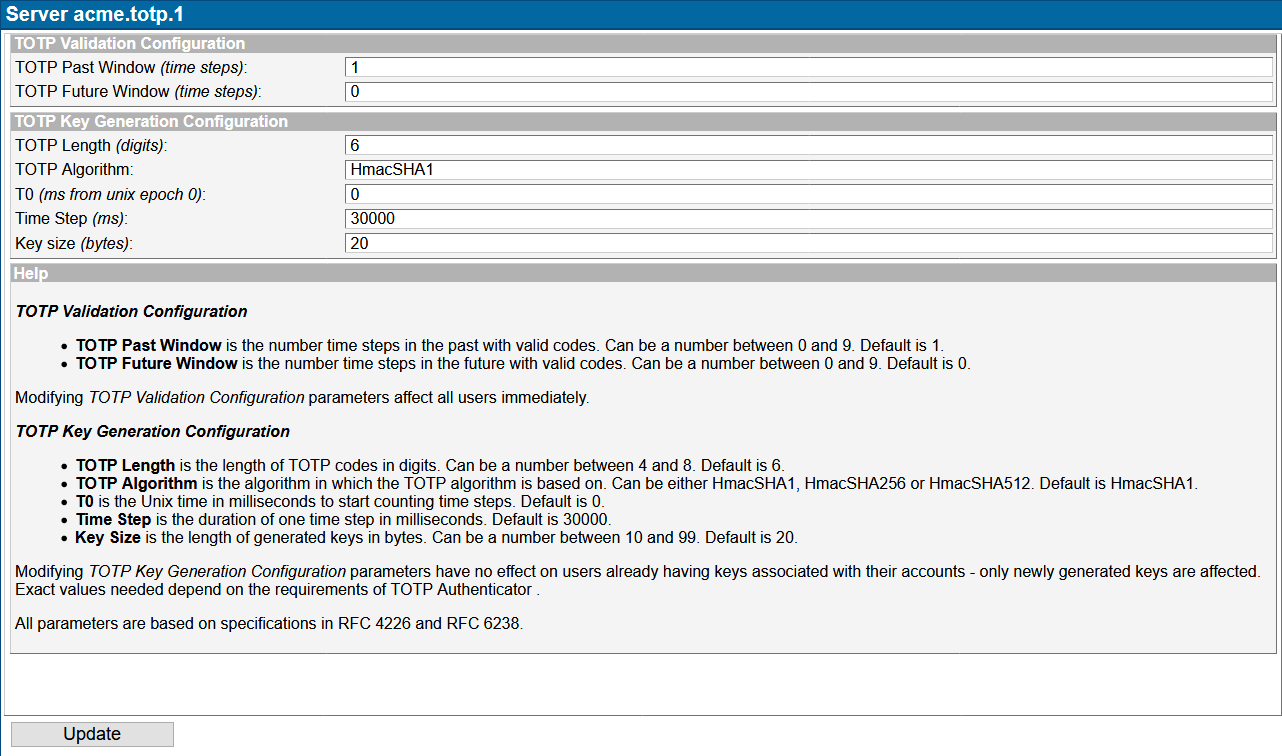
SPI TOTP
The configuration window for SPI TOTP authentication method is presented below.
| Figure 11: Configuring TOTP authentication method |
Please refer to TOTP Authentication Method for installing and configuring the TOTP authentication method.
SPI Ubisecure OTP Printout
The configuration window for SPI Ubisecure OTP Printout authentication method is presented below.
| Figure 12: Configuring Ubisecure OTP Printout authentication method |
Please refer to OTP Printout authentication method - SSO for installing and configuring the Ubisecure OTP Printout authentication method. If Ubisecure OTP is used in conjunction with an external directory, please refer one of the following guides:
Tupas 2
The configuration window for Tupas 2 type of authentication method is presented below.
| Figure 13: Configuring Tupas 2 authentication method |
Please refer to Installing the TUPAS authentication method - SSO for instructions on installing and configuring the Tupas 2 authentication method.
Discovery Service
The configuration window for Discovery Services is presented below. Configuration is made in the Configuration String setting. Both external SAML Discovery Services (also known as Where Are You From or WAYF services) and Common Domain Cookie discovery are supported. Service Discovery is part of Ubisecure Trust.
Using an External Discovery service, the end user selects their desired Identity Provider using a third-party service. Federation networks such as Haka, Virtu and e-Legitimation offer external discovery services.
Using Common Domain Cookie discovery, the system can silently detect if the user has an existing session at a trusted third-party IDP and if so, forward authentication requests there.
| Figure 14: Configuring an External discovery method |
Please refer to the pages
for instructions on installing and configuring the Discovery Services methods.
SAML
The SAML method permits configuration of a SAML Service Provider in an SAML Identity Provider Proxy configuration. The SAML Method permits an identity from a third-party system to be used on the local system. The SAML Method when used for federation a third-party system is part of the Ubisecure Trust product.
The configuration window for the SAML method type is presented below.
| Figure 15: Configuring a SAML authentication method |
Please refer to the page SAML IDP Proxy - SSO for instructions on installing and configuring the SAML methods. Users will access Web Applications configured on this Ubisecure SSO by logging in to a third-party IDP Server first.
The opposite direction, in other words, adding a SAML Service Provider Application to this Ubisecure SSO, is described in page Management UI Applications - SSO .
OAuth 2.0
The OAuth 2.0 method permits configuration to Ubisecure SSO to act as a OAuth 2.0 Client in a OAuth 2.0 based use case configuration, eg to to enable external authentication based on authentication of users by certain social media services.
The The Ubisecure OAuth 2.0 Client is currently implemented specifically to enable authentication for users of certain social media services and the protocols are implemented from this standpoint. For more information please refer to the OAuth2 - SSO pages
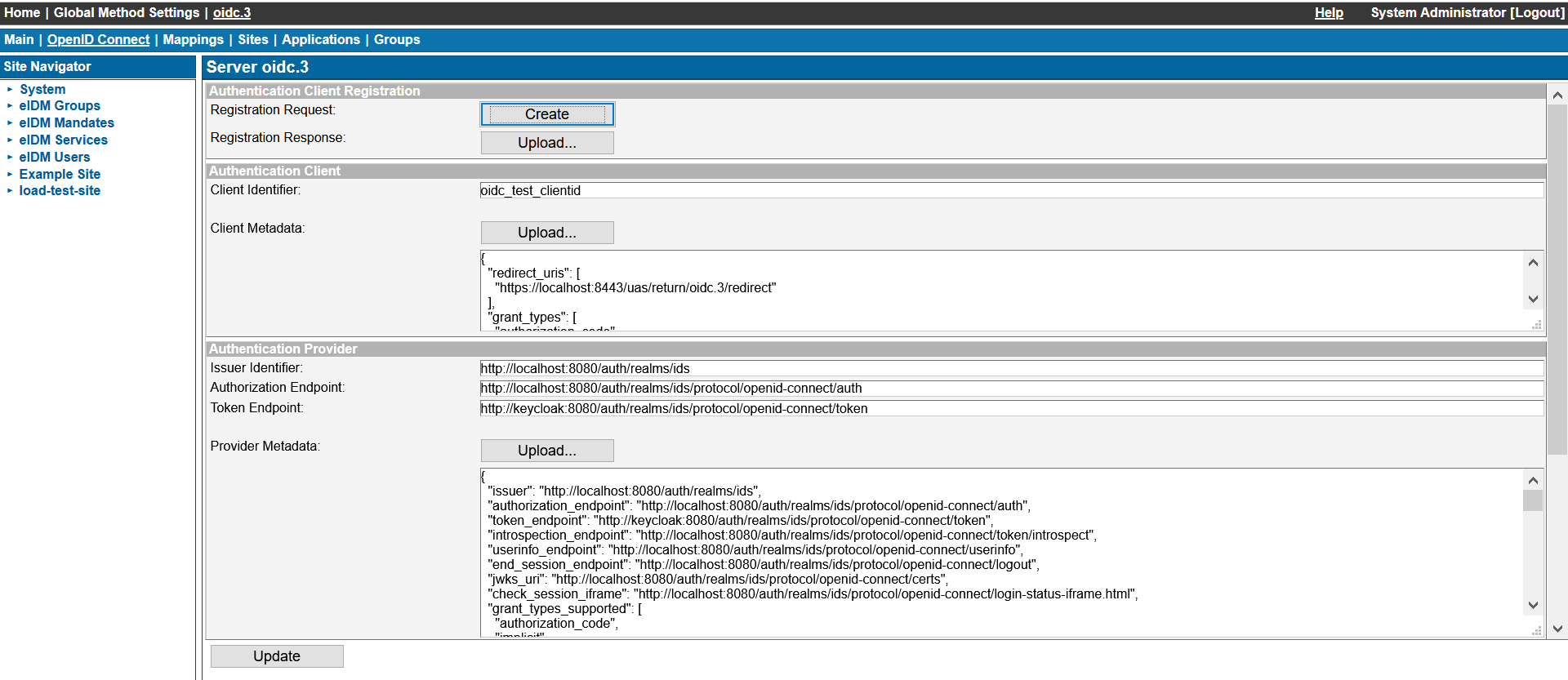
OpenID Connect
This method allows you to configure Ubisecure SSO as an OpenID Connect Relying Party where the authentication is delegated to an external OpenID Connect Provider. Please refer to OpenID Connect authentication method - SSO for more details.
| Figure 16: Configuring a OpenID Connect method |
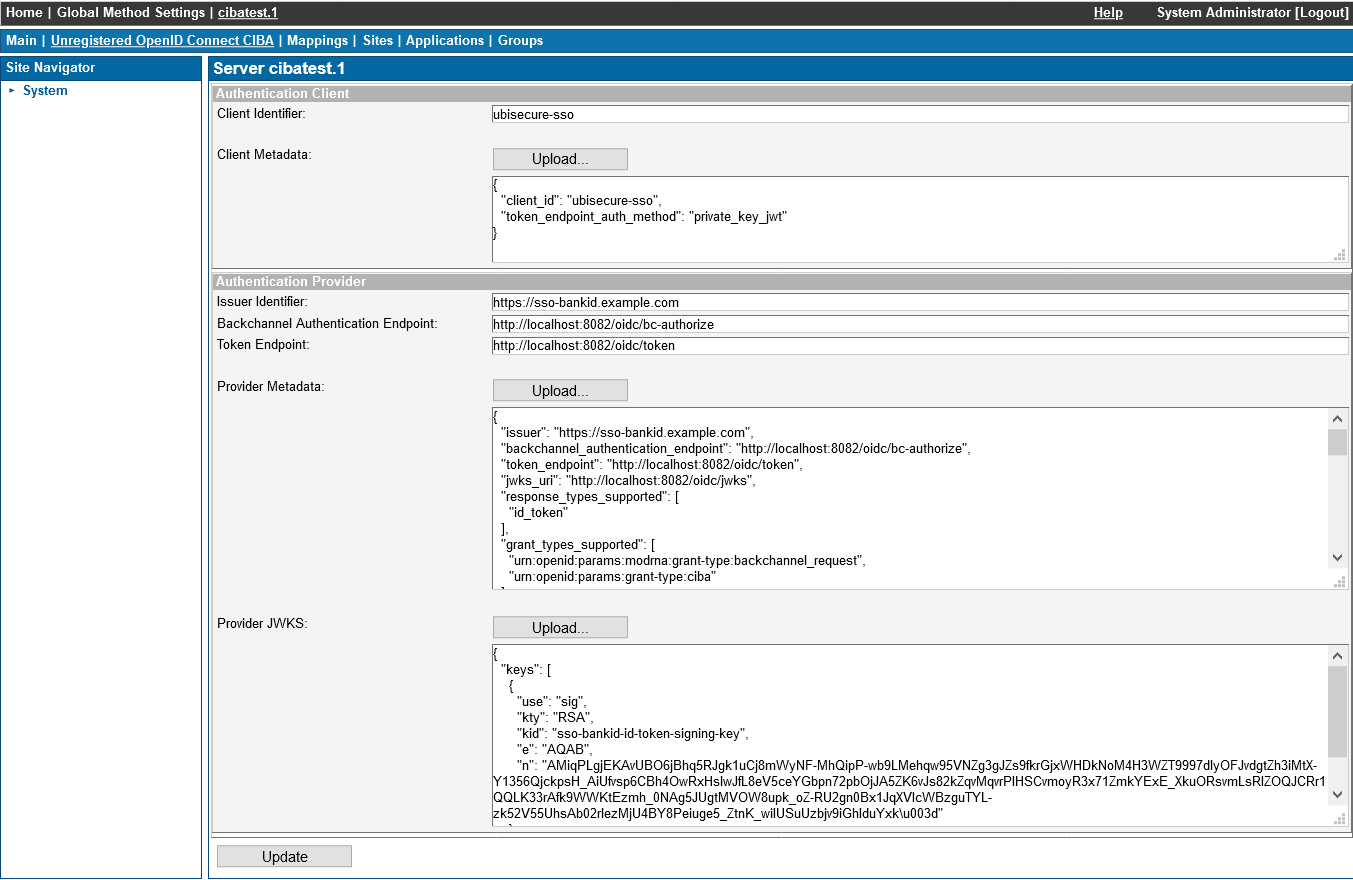
SPI OpenID Connect CIBA / Unregistered OpenID Connect CIBA
These method types allow using SSO CIBA Adapter for authenticating users. Please refer to OpenID Connect CIBA authentication method for more information.
| Figure 17: Configuring a OpenID Connect CIBA authentication method |
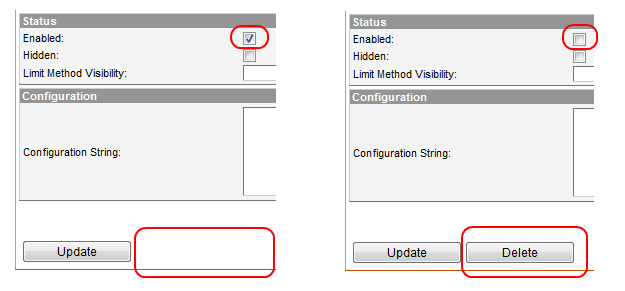
Deleting a Method
In order to delete an authentication method, it needs to be disabled first. Once disabled, the method can be deleted by clicking delete button in the configuration window.
| Figure 18: Deleting an authentication method |
Note that the Delete button does not appear until you disable the method and press Update.